Bangladesh Bank theft shines light on cyber risk
Banks and regulators increasingly concerned amid high-profile cyber security breaches

In the wake of the Bangladesh Bank theft, which saw cyber criminals steal $81 million from the Asian central bank, financial institutions and regulators worldwide are ramping up their efforts to defend against cyber threats.
“Regulators are asking us how we are handling information security; how we ensure that the second line has the necessary oversight and that the first line consolidates those efforts on a daily basis,” says one chief operational risk officer at a European bank.
In the ‘three lines of defence’ approach to risk governance, the first line comprises those who work in front-line business roles; the second line consists of the risk management function; and the third line corresponds to internal auditors.
Bangladesh Bank suffered its loss in February, when one of the central bank’s computer systems was compromised and used to execute a series of transfers from an account at the Federal Reserve Bank of New York. The New York Fed transferred $101 million to fictitious accounts at Rizal Commercial Banking Corporation (RCBC) in the Philippines and Pan Asia Bank in Sri Lanka before it became suspicious and denied the remaining 30 requests.
Bangladesh Bank recovered the funds from Sri Lanka, but RCBC released $81 million to a foreign exchange broker. Criminals smuggled some of the money out of the country, and laundered the rest through local casinos.
The transfers were ordered via the Swift messaging system. On May 13, Belgium-based Swift revealed that another of its client banks had been compromised in a way that shared characteristics with the Bangladesh Bank loss; specifically, hackers carried out a targeted attack using malware to circumvent banks’ secondary controls.
“Forensic experts believe this new discovery evidences that the malware used in the earlier reported customer incident was not a single occurrence, but part of a wider and highly adaptive campaign targeting banks,” the organisation says in a statement. The client involved was not named.
In light of these high-profile incidents, regulators are increasingly probing banks about their vulnerabilities. “Banks have such a huge amount of data, often just sitting in the dark and forgotten about,” says Paula Barrett, global head of privacy and information law at UK law firm Eversheds. “Regulators are asking about their remediation plans; about what they would do if they experienced a breach; and if they actively test the extent to which their customers could be impacted.”
Regulators are also becoming savvier when it comes to examining specific cyber security processes, she says. “They’re now looking at it from a totality perspective. Further to encryption and technological controls, they’re asking about training, access controls, and why a bank has chosen a particular service provider.”
Banks are being urged to adopt approaches such as the Framework for Improving Critical Infrastructure Cybersecurity, developed by the US National Institute of Standards and Technology. The framework includes an assessment of best practice that goes beyond IT to include people, processes and other sources of risk. Experts say banks should be identifying and quantifying the likely impact of cyber threats, as well as regularly testing their responses and risk controls.
Mark Camillo, global head of cyber at New York-based insurance giant AIG, says it is important firms understand their exposures to cyber to identify any gaps in their systems. “We often hear from regulators and intelligence agencies that over 80% of breaches could have been reasonably prevented by simple-to-intermediate controls, such as regularly patching your systems and application white-listing,” he says. “Some of these things are very basic and every company knows they should do them, but it seems that some just fall through the cracks and that’s when you end up having a compromise.”
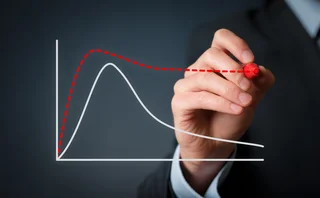
During recent years, many banks have been increasing the scope of their cyber security arrangements. In the Bank of England’s latest Systemic Risk Survey, released in December last year, 46% of respondents highlighted cyber risk as a key concern. That compares with just 10% a year earlier (see figure).
 The chief op risk officer at the European bank says his firm is now applying its cyber risk framework as it develops new products, instead of simply reacting to threats as they emerge. “The more you can implement and enhance your product during the change approval process, the more you can start working on mitigating your identified risk,” he says. “Of course, if you don’t have those formalised frameworks, you don’t get your risk identified in the right way and then you can’t mitigate it.”
The chief op risk officer at the European bank says his firm is now applying its cyber risk framework as it develops new products, instead of simply reacting to threats as they emerge. “The more you can implement and enhance your product during the change approval process, the more you can start working on mitigating your identified risk,” he says. “Of course, if you don’t have those formalised frameworks, you don’t get your risk identified in the right way and then you can’t mitigate it.”
Still, there’s more that banks can do. A joint report published on May 17 by risk specialists Marsh and industry group TheCityUK proposed the creation of a forum focused on systemic cyber risk reduction. The forum would include a steering group of board-level representatives from the financial industry, as well as a working group of risk managers and chief information security officers. The idea is to promote information-sharing and bring cyber issues to the direct attention of senior business leaders.
One particular area of concern is risk aggregation. The report emphasised the importance of mapping tools to track the technological linkages between different firms. The fear is that these linkages could be a source of systemic contagion, similar to the blight caused by US subprime mortgages during the financial crisis.
“Seemingly independent firms may turn out to share common exposure to cyber risk by dint of common suppliers or customers, or by using common service providers and infrastructure,” the report said. “[Cyber risk aggregation tools] give at least a basis for starting to address the problem of how cyber risk might accumulate in the financial system.”
“The cyber threat is a shared issue,” said John MacFarlane, chairman of Barclays, speaking at the unveiling of the report in London on May 17. “Of course, as firms we need to make ourselves as secure as possible. But there is limited advantage in going alone... We as governments, firms and individuals need to have an integrated response.”
Only users who have a paid subscription or are part of a corporate subscription are able to print or copy content.
To access these options, along with all other subscription benefits, please contact info@risk.net or view our subscription options here: http://subscriptions.risk.net/subscribe
You are currently unable to print this content. Please contact info@risk.net to find out more.
You are currently unable to copy this content. Please contact info@risk.net to find out more.
Copyright Infopro Digital Limited. All rights reserved.
As outlined in our terms and conditions, https://www.infopro-digital.com/terms-and-conditions/subscriptions/ (point 2.4), printing is limited to a single copy.
If you would like to purchase additional rights please email info@risk.net
Copyright Infopro Digital Limited. All rights reserved.
You may share this content using our article tools. As outlined in our terms and conditions, https://www.infopro-digital.com/terms-and-conditions/subscriptions/ (clause 2.4), an Authorised User may only make one copy of the materials for their own personal use. You must also comply with the restrictions in clause 2.5.
If you would like to purchase additional rights please email info@risk.net
More on Risk management
Hopes, fears and ‘mass confusion’: the sudden end of SR 11-7
Banks welcome chance to prioritise model reviews, but fret over future policy changes and AI
Bootcamps and peer pressure: Goldman preps staff for AI future
Isda AGM: Tone from the top is not enough, says chief information officer Marco Argenti
In Iran war, VAR models ease cliff effect on Ice and CME margins
At 105%, EEX – using Span model – saw largest single-day jump compared with those CCPs
MRM: how banks are scaling models in the age of AI
MRM capabilities are evolving to ensure compliance while helping organisations retain a competitive edge
ALM in 2026: the fast-track from compliance to competitive edge
How banks are modernising asset-liability management for a more volatile world
Why AI-related conduct risk is reshaping the business agenda
Trust in AI-only approaches remains limited, and explainability is becoming critical to modern risk management
NeoClear enters battle for euro swaps clearing
Paris-based CCP to challenge Eurex and LCH with planned 2027 launch
Abaxx: meeting the need for new commodity derivatives
Abaxx revamps commodity hedging with a suite of modern contracts